What Is ZTNA?
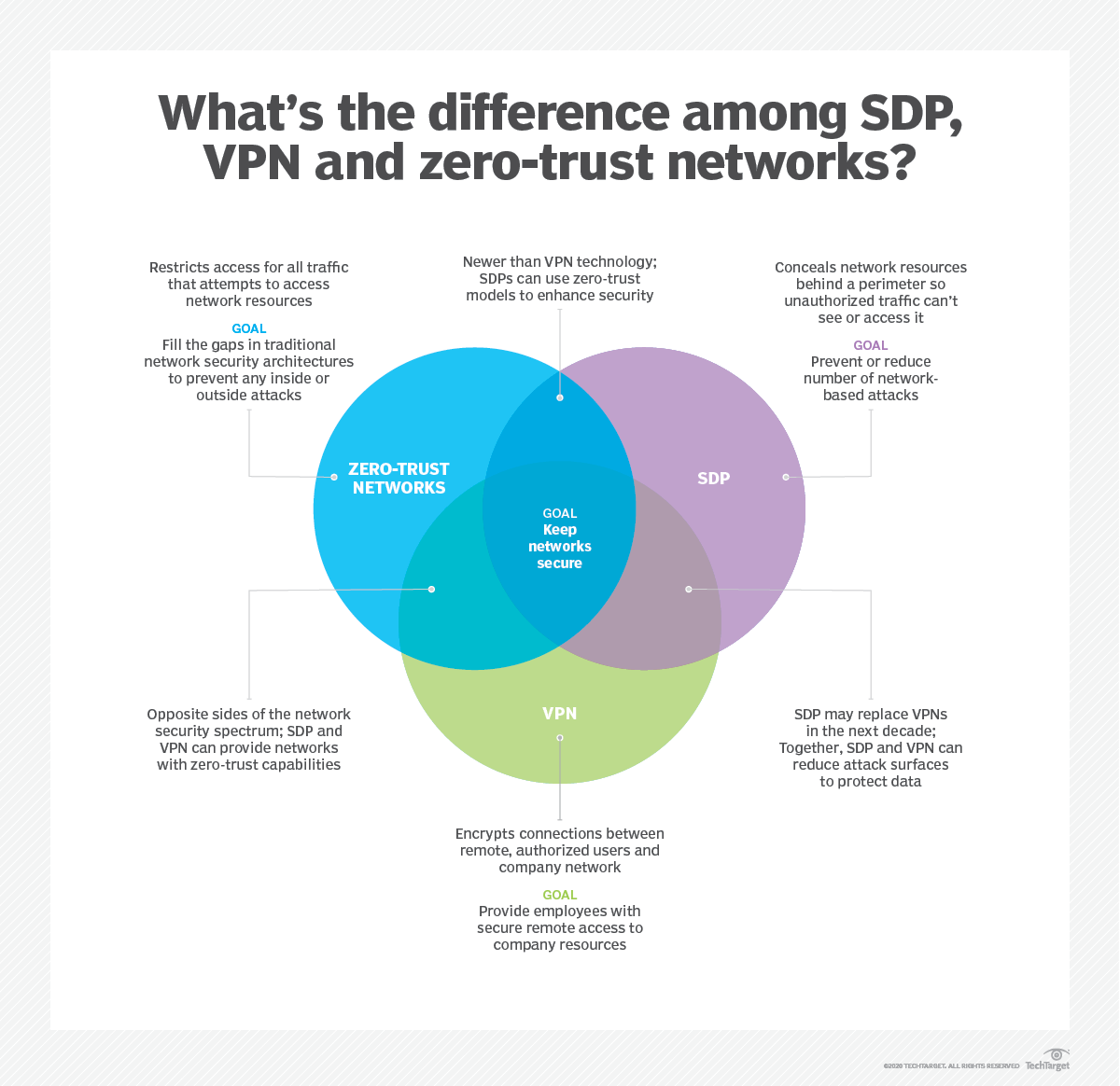
Zero trust network access (ZTNA), also known as the software-defined perimeter (SDP), is a set of technologies and functionalities that enable secure access to internal applications for remote users. It operates on an adaptive trust model, where trust is never implicit, and access is granted on a need-to-know, least-privileged basis defined by granular policies. ZTNA gives remote users seamless, secure connectivity to private applications without ever placing them on the network or exposing apps to the internet.
Zero trust security is a big buzzword these days. While many organizations have shifted their priorities to adopt zero trust, zero-trust network access (ZTNA) is the strategy behind achieving an effective zero trust model.
The path to zero trust as an ideology is vague, so ZTNA provides a clear, defined framework for organizations to follow. It’s also a component of the secure access service edge (SASE) security model, which, in addition to ZTNA, comprises next-gen firewall (NGFW), SD-WAN, and other services in a cloud-native platform.
How Does ZTNA Work?
While the need to secure a remote workforce has become critical, network-centric solutions such as virtual private networks (VPNs) and firewalls create an attack surface that can be exploited. ZTNA takes a fundamentally different approach to providing secure remote access to internal applications based on these four core principles.
- ZTNA completely isolates the act of providing application access from network access. This isolation reduces risks to the network, such as infection by compromised devices, and only grants access to specific applications for authorized users who have been authenticated.
- ZTNA makes outbound-only connections ensuring both network and application infrastructure are made invisible to unauthorized users. IPs are never exposed to the internet, creating a “darknet” that makes the network impossible to find.
- ZTNA’s native app segmentation ensures that once users are authorized, application access is granted on a one-to-one basis. Authorized users have access only to specific applications rather than full access to the network. Segmentation prevents overly permissive access as well as the risk of lateral movement of malware and other threats.
- ZTNA takes a user-to-application approach rather than a traditional network security approach. The network becomes deemphasized, and the internet becomes the new corporate network, leveraging end-to-end encrypted TLS micro-tunnels instead of MPLS.
Gartner, Market Guide on Zero Trust Network Access, April 2019
From an architectural perspective, ZTNA works fundamentally differently from network-centric solutions. ZTNA is most often 100% software-defined, eliminating the overhead of managing appliances. ZTNA also helps organizations simplify inbound stacks as they no longer require their VPN and VPN concentrators, DDoS protection, global load balancing, and firewall appliances.
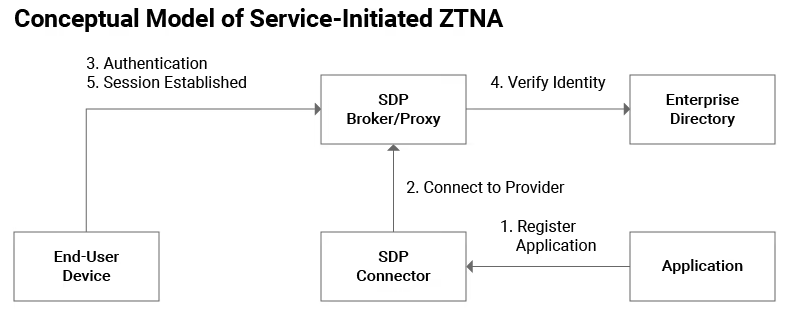
There are two key ZTNA architecture models. This article highlights the service-initiated ZTNA architecture below. Read Gartner’s ZTNA Market Guide for more details.
What’s the Difference Between VPN and ZTNA?
Among the most popular legacy security solutions in use today, VPNs are meant to simplify access management by allowing end users to securely access a network, and therefore corporate resources, through a designated tunnel, usually through single sign-on (SSO).
For many years, VPNs worked well for employees who needed to work remotely for a day or two, but as the world saw more and more long-term remote workers, these VPNs became ineffective due to their lack of scalability and the extreme amount of maintenance (and cost) to keep them running. What’s more, the rapid adoption of the public cloud meant that it not only became more difficult to apply security policies to this new breadth of remote workers but also hurt the user experience.
The main problem with VPNs, however, is the attack surface they create. Any user or entity with the necessary SSO credentials can log on to a VPN and move laterally throughout the network, giving them access to all the resources and data the VPN was meant to protect.
ZTNA secures user access by granting it on the principle of least privilege. Rather than trusting on the basis of correct credentials, zero trust authenticates only under the correct context—that is, when the user, identity, device, and location all match up.
Furthermore, ZTNA provides granular access rather than network access. Users are connected directly and securely to the applications and data they need, which prevents the possibility of lateral movement by malicious users. Plus, because user connections are direct, experiences are vastly improved when leveraging a ZTNA framework.
Top ZTNA use cases
ZTNA has many cloud security use cases. Most organizations choose to start with one of these four.
VPN alternative
VPNs are inconvenient and slow for users, offer poor security, and are difficult to manage, so organizations want to reduce or eliminate their reliance on them. Gartner predicts: “By 2023, 60% of enterprises will phase out most of their remote access VPNs in favor of ZTNA.”
Secure multi-cloud access
Securing hybrid and multi-cloud access is the most popular place for organizations to start their ZTNA journey. With more companies adopting cloud applications and services, 37% of them are turning to ZTNA for security and access control for their multi-cloud strategies.
Reduce third-party risk
Most third-party users receive overprivileged access, and they largely access applications using unmanaged devices, both of which introduce risks. ZTNA significantly reduces third-party risk by ensuring external users never gain access to the network and that only authorized users can access allowed applications.
Accelerate M&A integration
With typical M&As, integration can span multiple years as organizations converge networks and deal with overlapping IPs. ZTNA reduces and simplifies the time and management needed to ensure a successful M&A and provides immediate value to the business.
Considerations for ZTNA
In Gartner’s recent Market Guide on Zero Trust Network Access, Steve Riley, Neil MacDonald, and Lawrence Orans outline several things organizations should consider when choosing a ZTNA solution:
- Does the vendor require an endpoint agent to be installed? What OSs are supported? What mobile devices? How well does the agent behave in the presence of other agents? Note: ZTNA technologies that do not support clientless use often can’t support unmanaged device use cases (e.g., third-party access, BYOD).
- Does the offering support only web applications, or can legacy (data center) applications gain the same security advantages?
- Some ZTNA products are delivered partly or wholly as cloud-based services. Does this meet the organization’s security and residency requirements? Note: Gartner recommends that enterprises favor vendors that offer ZTNA as a service, as services are easier to deploy, more available, and provide better security against DDoS attacks.
- To what extent is partial or full cloaking, or allowing or prohibiting inbound connections, a part of the isolated application’s security requirements?
- What authentication standards does the trust broker support? Is integration with an on-premises directory or cloud-based identity services available? Does the trust broker integrate with the organization’s existing identity provider?
- How geographically diverse are the vendor’s entry and exit points (referred to as edge locations and/or points of presence) worldwide?
- After the user and user device pass authentication, does the trust broker remain resident in the data path?
- Does the offering integrate with unified endpoint management (UEM) providers, or can the local agent determine device health and security posture as factors in the access decision? What UEM vendors has the ZTNA vendor partnered with?
These are all important considerations for your enterprise as you look for the ZTNA vendor that complements your present and forward-looking goals and vision.